By Raymond Brooks
As a senior consultant with expertise in Microsoft Azure, Microsoft Exchange, Office 365, and Active Directory, I have seen firsthand how security threats continue to evolve and challenge organizations worldwide. In today’s ever-changing cyber landscape, it is crucial for businesses to stay one step ahead of potential attackers. To achieve this, Microsoft has developed an innovative solution called Microsoft 365 Attack Simulation Training. In this blog post, I will dive into the inner workings of this powerful tool and explain how it can bolster your organization’s cybersecurity efforts.
Microsoft 365 Attack Simulation Overview
Microsoft 365 Attack Simulation is a powerful tool designed to help organizations improve their cybersecurity defenses by simulating real-world attack scenarios. With this feature, organizations can identify vulnerabilities, train employees, and track their security performance over time, ultimately reducing the risk of potential data breaches and financial losses.
Addressing Key Customer Security Needs
Organizations can boost organization security by simulating real-world attack scenarios and users can learn how to identify and respond to potential threats, reducing the risk of a successful breach. This proactive approach to cybersecurity enables IT administrators to identify vulnerabilities, assess the effectiveness of their security policies. Therefore, their users become better educated on recognizing and responding to potential threats.
The simulation platform offers various attack scenarios, including phishing, password spray, and brute force attacks. By simulating these attacks, organizations can gather valuable insights into their security posture and take necessary steps to strengthen their defenses.
Key Benefits of Attack Simulation Training
Identify Vulnerabilities and Enhance Security Policies
By having this solution, you can provide a realistic simulation of real-world attack scenarios, and the ability to provide detailed reporting and analytics to track the effectiveness of training efforts. Therefore, IT professionals can identify potential weaknesses and make necessary adjustments to improve their overall security posture.
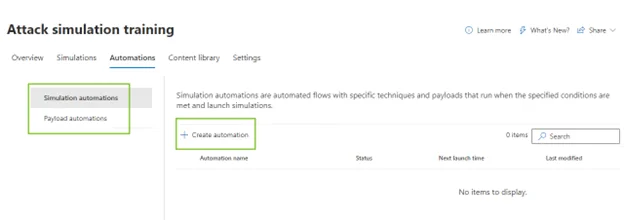
Attack Simulation Automation
A major benefit of Attack Simulation Automation is that it allows organizations to continuously test their cybersecurity defenses against various attack scenarios automatically, without the need for manual intervention. This can save time and resources while providing up-to-date information on the effectiveness of security measures. Such actions also help organizations to identify and address vulnerabilities in their systems before an actual attack occurs.
Educate Users on Security Best Practices
One of the most significant challenges organizations face when it comes to cybersecurity is ensuring that users are aware of the potential risks and know how to respond to them effectively. Attack Simulation Training enables organizations to educate their users about common attack methods and tactics, helping them identify and avoid potential threats.
Get Insights Into User Behavior
By monitoring user behavior during simulated attacks, IT administrators can identify individuals who may be more susceptible to real-life attacks. This information can be used to provide targeted training and support, ensuring that all users are adequately prepared to face potential threats. Click here to see what additional insights you can gain with new data points.
A Step-by-Step Guide to Launching an Attack Simulation
- Get started with the Microsoft 365 Defender portal and navigate to the “Attack Simulation Training” section.
- Under Email & Collaboration, select Attack simulation training, then Simulations, then Launch simulation. Credential harvesting is popular among hackers because it’s a simple and effective way to steal login information and gain access to sensitive accounts. Many people use the same login credentials across multiple accounts, making it easy for attackers to gain access to multiple accounts at once. Idea simulation is achieved.
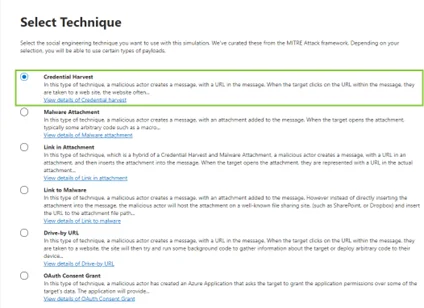
- Then provide an easily identifiable name for you simulation. Microsoft gives numerous Credential Harvesting templates to choose from, each can be previewed by sending a test email to the administrator.
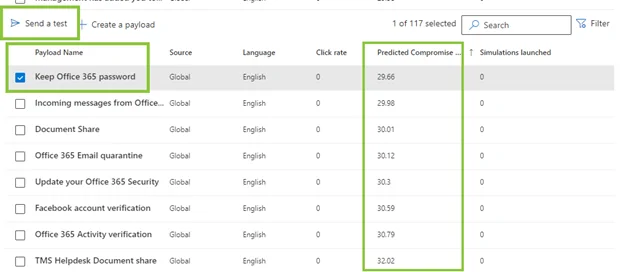
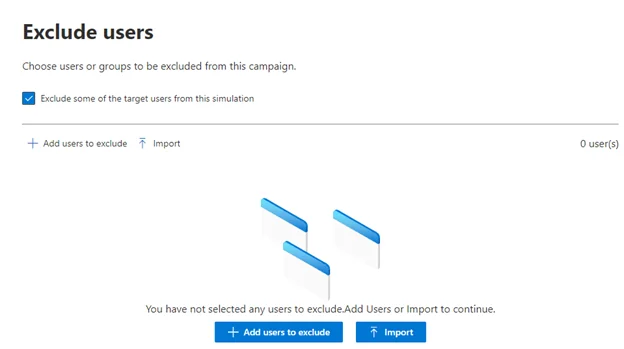
- Customize the simulation settings, including the target user groups, the scope of the attack, and the level of difficulty. You can also exclude specific users or groups.
- Several options are provided when it comes to training. For example, you can use the recommended method where Microsoft provides not only the training material but also the specific material based on the template used, or you can select multiple Microsoft training content.
- If the user clicks the phishing link, we need to redirect them to our phishing page, to do this we need to select phishing landing page.
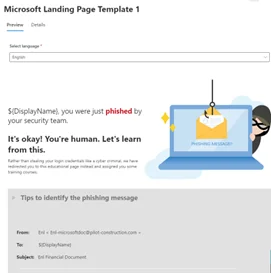
There is the option of providing your own custom link or selecting from pre-made templates provided by Microsoft. These templates come in various languages and allow you to include company branding.
- Schedule the simulation to launch at a specific date, as well as for how long, considering time zone differences, or initiate it immediately.
- Finally, you can send a test email to ensure everything is set up correctly before submitting the campaign to be run.
- Monitor the progress of the simulation in real-time and analyze the results once it’s complete.
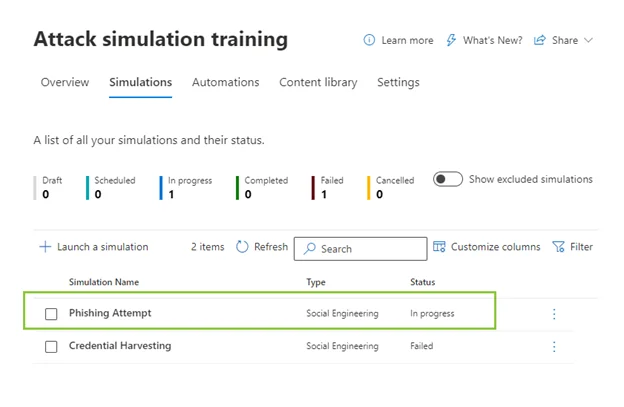
- Review the detailed reports generated by the simulation, which provide insights into user behavior, vulnerabilities, and the effectiveness of your security policies.
- Use the findings from the simulation to enhance your organization’s security posture, educate users, and improve incident response capabilities.
Leverage this Powerful Tool
As a senior consultant, I highly recommend leveraging Attack Simulation Training to fortify your organization’s cyber defenses and stay ahead of the ever-evolving threat landscape.
If you’re interested in learning more about how Attack Simulation Training can help your organization become more secure, don’t hesitate to connect with our consultants. Our team of experts can help you implement the training with qualified step-by-step guidance to educate your employees about common attack methods, and improve your organization’s defense.
Contact us today to get started!